As I told you all yesterday, and why I'm poo pooing at the "evidence" - doubt you'll see this one in the MSM but folks who know anything about IT security (or hacking) are scratching their heads (and/or laughing at partisan tantrums) -
US Govt Data Shows Russia Used Outdated Ukrainian PHP Malware
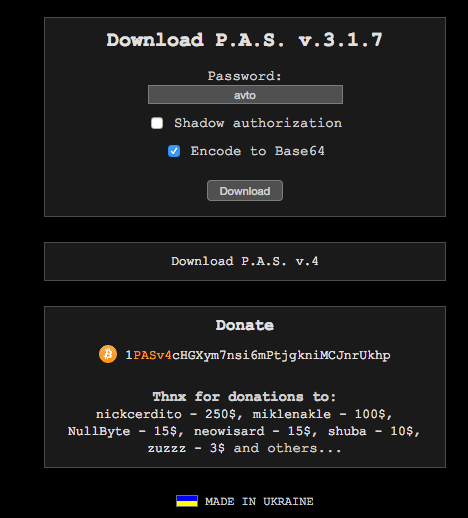
By viewing the source code, we could find the name of the malware and the version. It is P.A.S. 3.1.0.
We googled it and found a website that makes this malware. You can find the site at this address:
Download P.A.S. v.3.1.7
<see source site for pic>
You can enter a password that you will use to access your malware once it’s installed and then hit ‘download’ and a ZIP file downloads.
Malware Conclusions
DHS and DNI have released a joint statement that says:
“This document provides technical details regarding the tools and infrastructure used by the Russian civilian and military intelligence Services (RIS) to compromise and exploit networks and endpoints associated with the U.S. election, as well as a range of U.S. Government, political, and private sector entities. The report contains specific indicators of compromise, including IP addresses and a PHP malware sample.”
The PHP malware sample they have provided appears to be P.A.S. version 3.1.0 which is commonly available and the website that claims to have authored it says they are Ukrainian. It is also several versions behind the most current version of P.A.S which is 4.1.1b. One might reasonably expect Russian intelligence operatives to develop their own tools or at least use current malicious tools from outside sources.
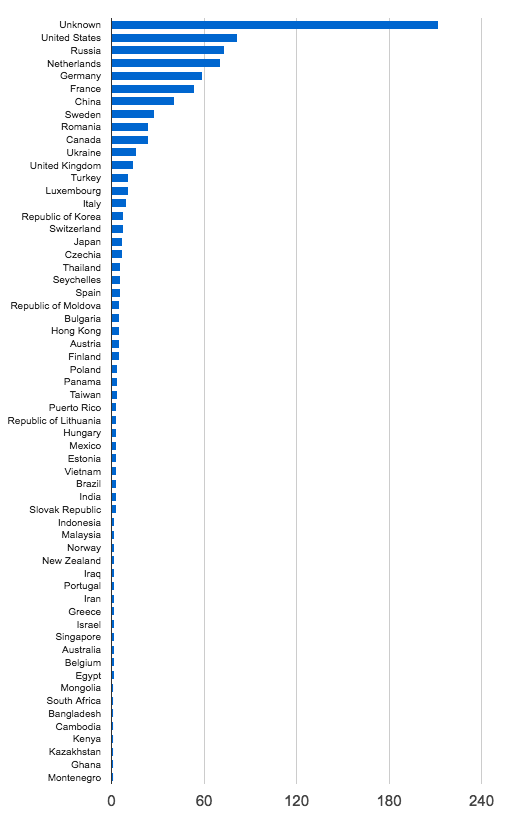
DHS provided us with 876 IP addresses as part of the package of indicators of compromise. Lets look at where they are located. The chart below shows the distribution of IP addresses by country.
<See source site for pic>
As you can see they are globally distributed with most of them in the USA.
Lets look at who the top ISP’s are who own the IP addresses:
<see source site for pic>
There are several hosting companies in the mix including OVH SAS, Digital Ocean, Linode and Hetzner. These are hosting companies that provide low cost hosting to WordPress customers and customers who use other PHP applications. A common pattern that we see in the industry is that accounts at these hosts are compromised and those hacked sites are used to launch attacks around the web.
Out of the 876 IP addresses that DHS provided, 134 or about 15% are Tor exit nodes, based on a reverse DNS lookup that we did on each IP address. These are anonymous gateways that are used by anyone using the Tor anonymous browsing service.
We examined our attack data to see which IP addresses in the DHS data are attacking our customer websites. We found a total of 385 active IP addresses during the last 60 days. These IP addresses have launched a total of 21,095,492 complex attacks during that 60 day period that were blocked by the Wordfence firewall. We consider a complex attack to be an attack that tries to exploit a vulnerability to gain access to a target.
We also logged a total of 14,463,133 brute force attacks from these IP addresses during the same period. A brute force attack is a login guessing attack.
The chart below shows the distribution of the number of attacks per IP address. It only takes into account complex attacks. As you can see, a small number of the IP addresses that DHS provided as IOC’s are responsible for most of the attacks on WordPress websites that we monitor.
<see source site for pic>
The following shows the list of the top 50 IP addresses in the DHS report sorted by the number of complex attacks we saw from each IP during the past 60 days.
<see source site for pic>
As you can see, many of the top attacking IP addresses are Tor exit nodes. There is also a relatively small number of IP addresses launching most of the attacks on websites we monitor.
Conclusion regarding IP address data
What we’re seeing in this IP data is a wide range of countries and hosting providers. 15% of the IP addresses are Tor exit nodes. These exit nodes are used by anyone who wants to be anonymous online, including malicious actors.
Overall Conclusion
The IP addresses that DHS provided may have been used for an attack by a state actor like Russia. But they don’t appear to provide any association with Russia. They are probably used by a wide range of other malicious actors, especially the 15% of IP addresses that are Tor exit nodes.
The malware sample is old, widely used and appears to be Ukrainian. It has no apparent relationship with Russian intelligence and it would be an indicator of compromise for any website.
You can find a public repository containing the data used in this report on github.
As always I welcome your comments. Please note that I will delete any political comments. Our goal in this report is to merely analyze the data DHS provided and share our findings.