You mean the malware I have repeatedly posted the link where it is available to download? That malware
oreo? Yes, I'm quite sure it's been used in hundreds of thousands of hacks all over the planet.
Do you think that if the Russian government was creating a Malware for use in their espionage, they would throw it up on the web for white hackers to de-compile and add to their anti-virus definitions? I'm afraid I'm not that stupid.
Even /if/ you believe that level of stupid, when something is available to download via GOOGLE (aka how we found out it was PAS 3.1.0) that means that almost anyone could then use it to hack anyone else, military or civilian, North Korean, Chinese, Russian, Ukrainian, Romanian, American, European, Middle East, /anyone/ on the planet could be using it.
In order to tie the /specific/ attacks to Russia one would have to show some evidence that it was used at least from the country. Our stupid government can't even do that in their "evidence"! The US Government's OWN REPORT INDICATES OTHER COUNTRIES: ~
GRIZZLY STEPPE – Russian Malicious Cyber Activity
This is their CVS File on Indicators (aka "The JAR package offers technical details regarding the tools and infrastructure used by Russian civilian and military intelligence services (RIS). Accompanying CSV and STIX format files of the indicators are available here:
GRIZZLY STEPPE Indicators (
CSV)")
Here are screenshots of the first three pages worth of IPs and their countries of origin in the CSV file
OUR GOVERNMENT put out which shows pretty much every country on the planet, (if you have MS Excel or a text editor I encourage you to look at it yourself and verify it. [to view it with text you'd have to "open with" a text editor; notepad or similar])
Again, see -
US Govt Data Shows Russia Used Outdated Ukrainian PHP Malware
DHS provided us with 876 IP addresses as part of the package of indicators of compromise.
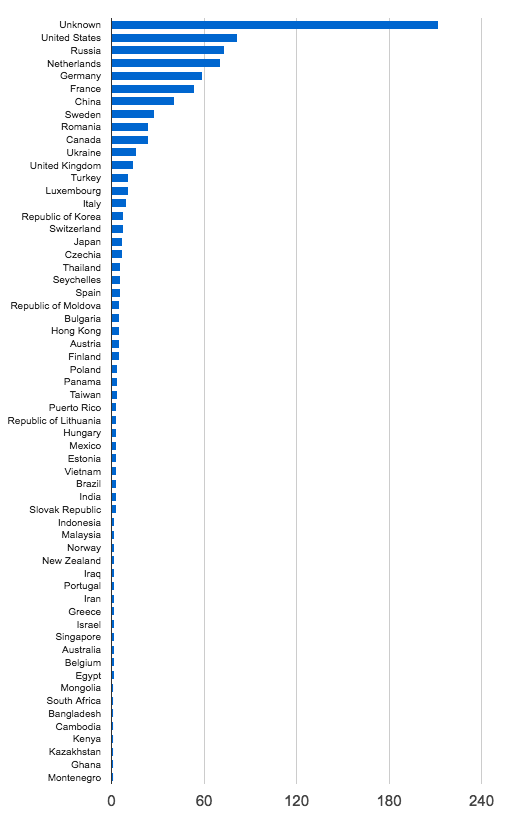
[aka the CSV I showed some of above] Lets look at where they are located. The chart below shows the distribution of IP addresses by country.
As you can see they are globally distributed with most of them in the USA.
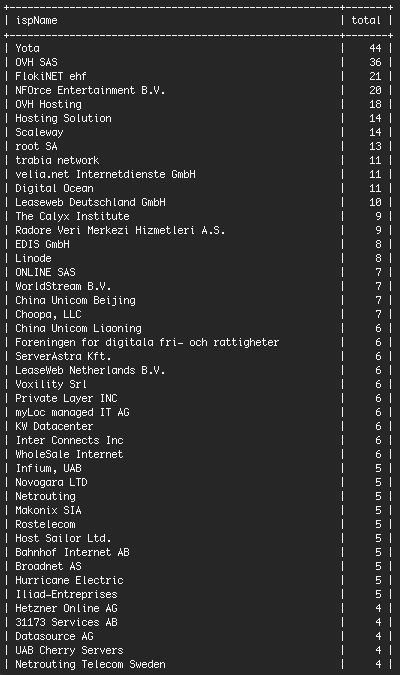
Lets look at who the top ISP’s are who own the IP addresses:
There are several hosting companies in the mix including OVH SAS, Digital Ocean, Linode and Hetzner. These are hosting companies that provide low cost hosting to WordPress customers and customers who use other PHP applications. A common pattern that we see in the industry is that accounts at these hosts are compromised and those hacked sites are used to launch attacks around the web.
Out of the 876 IP addresses that DHS provided, 134 or about 15% are Tor exit nodes, based on a reverse DNS lookup that we did on each IP address. These are anonymous gateways that are used by anyone using the Tor anonymous browsing service.
https://www.wordfence.com/wp-content/uploads/2016/12/Screen-Shot-2016-12-30-at-3.41.37-AM.png
---
Do you not understand TOR? -
Tor Project: Overview
Tor helps to reduce the risks of both simple and sophisticated traffic analysis by distributing your transactions over several places on the Internet, so no single point can link you to your destination. The idea is similar to using a twisty, hard-to-follow route in order to throw off somebody who is tailing you — and then periodically erasing your footprints. Instead of taking a direct route from source to destination, data packets on the Tor network take a random pathway through several relays that cover your tracks
so no observer at any single point can tell where the data came from or where it's going.
Do you not understand IP masking? -
How to Hide Your IP Address - 3 Easy Ways
Top 4 reasons why people want to hide their IP address:
Hide their geographical location
Prevent Web tracking
Avoid leaving a digital footprint
Bypass any bans or blacklisting of their IP address
Do you not understand virtual IPs? -
Virtual IP address - Wikipedia
A virtual IP address (VIP or VIPA) is an IP address that
doesn't correspond to an actual physical network interface (port). Uses for VIPs include network address translation (especially, one-to-many NAT), fault-tolerance, and mobility.
See also -
Tor - Free downloads and reviews - CNET Download.com
Ip Mask - Free downloads and reviews - CNET Download.com
Virtual Ip - Free downloads and reviews - CNET Download.com